Simple Ways Businesses Can Strengthen Cybersecurity and Reduce Risk The Hidden Risk Most Businesses Overlook When most people think about cybersecurity, they picture ransomware, hackers, or major data breaches making headlines. What many businesses miss is...
Latest Blog
Blogs
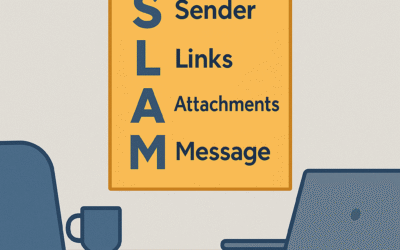
How to Use the SLAM Method to Spot Phishing Emails Before It’s Too Late
Learn how to stop phishing scams with the SLAM method. A simple 4-step checklist—Sender, Links, Attachments, Message—helps employees quickly spot suspicious emails before it’s too late.
Stuck on ‘Printing’ But Nothing Happens? How to Clear the Print Queue in Windows
Printer stuck on ‘Printing’? Learn how to quickly clear the print queue in Windows, restart the spooler, and fix common issues—without waiting on IT support.
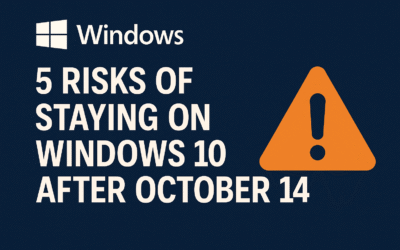
5 Risks of Staying on Windows 10 After October 14
Microsoft ends support for Windows 10 on October 14, 2025. Here are 5 major risks of staying on it—security, compliance, costs, and more—and why it’s time to upgrade now.
Why a Website Won’t Load — and How to Tell If It’s You or Them
Frustrated by a website that won’t load? Learn quick checks to see if the problem is your internet or the website itself—saving time, reducing stress, and keeping your business running smoothly.
Why Emails Disappear From Your Inbox — and How to Get Them Back
Emails don’t just vanish—they’re often filtered, archived, or accidentally deleted. Learn why messages disappear and how to recover them to keep your inbox reliable.
Windows 10 End of Support: What It Means for Your Business
Windows 10 support is ending soon. Learn what this means for your business, the risks of staying on outdated systems, and the smart steps to protect your company today.
Why Your Monitor Won’t Turn On — and How to Tell If It’s the PC or the Screen
Blank screen? Before you panic, learn how to tell if it’s your PC or just the monitor. Simple troubleshooting steps save time and help IT support solve your issue faster.
Why It’s Time to Upgrade from Microsoft 365 Business Standard to Business Premium
Business Standard gives you apps, but not the protection you need. Learn why upgrading to Business Premium adds security, compliance, and peace of mind for your business.
Laptop Won’t Connect to Wi-Fi? 5 Quick Fixes Anyone Can Try
Laptop won’t connect to Wi-Fi? Don’t panic—most fixes are simple. Here are 5 quick, non-technical solutions to get your laptop back online and keep your workday moving smoothly